In this blog post, I will demonstrate a simple Azure AD-protected Web API sample using Spring Boot Starter for Azure Active Directory. If you are not familiar with Spring Boot Starter for Azure Active Directory, please take a look at azure-sdk-for-java/sdk/spring/azure-spring-boot-starter-active-directory at main · Azure/azure-sdk-for-java (github.com) and the Azure AD Spring Developer’s Guide.
Requirement: You must have a Web API Application registered in Azure Active Directory and expose its permission scope (Delegated and/or Application). To understand the difference between Delegated and Application permission refer to difference between application permission and delegated permission | Azure Active Directory Developer Support Team (aaddevsup.xyz).
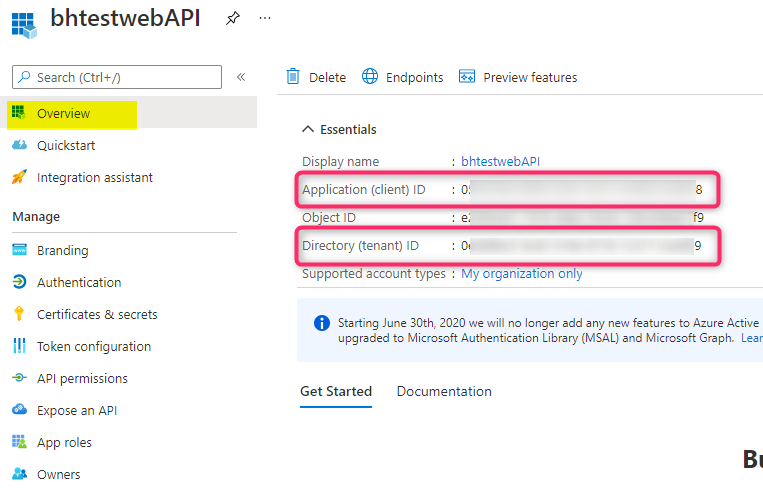
Below is my sample Web API app registration. In the overview blade, take note of both the Application (client) ID and the Directory (tenant) ID fields as you will need these to configure in the application.properties file.
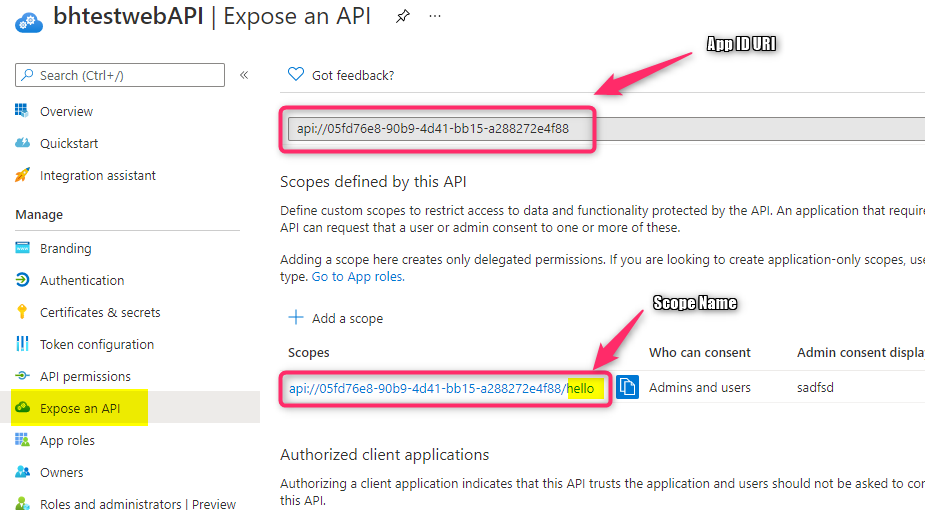
In this sample Web API, I’ll expose both types of permission. For delegated permission, use the ‘Expose an API’ blade. Set the App ID URI field if the value has not been set already. For my web API, I create a custom scope named ‘hello’. The fully qualified scope name is in this format: {App ID URI}/{scope name}. Take note of both the App ID URI and the scope name as we will need these for the project.
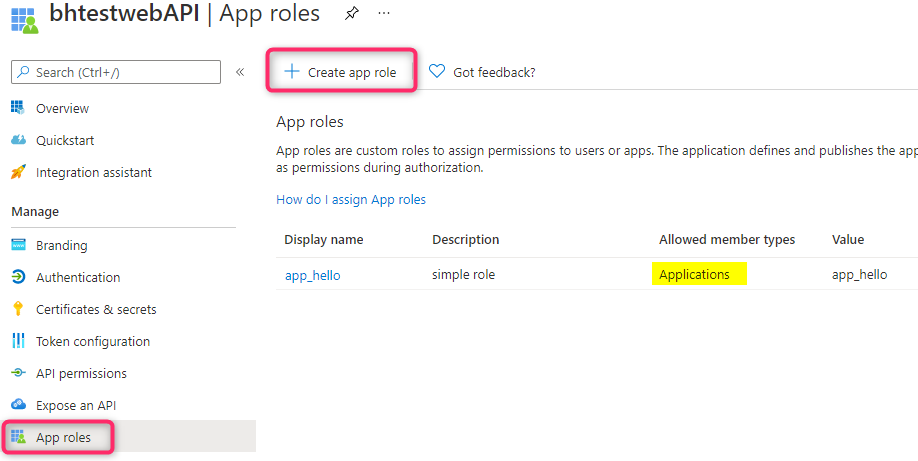
For application permission, I use the ‘App roles’ blade to create a permission scope named ‘app_hello’ with the allowed member types to be Applications.
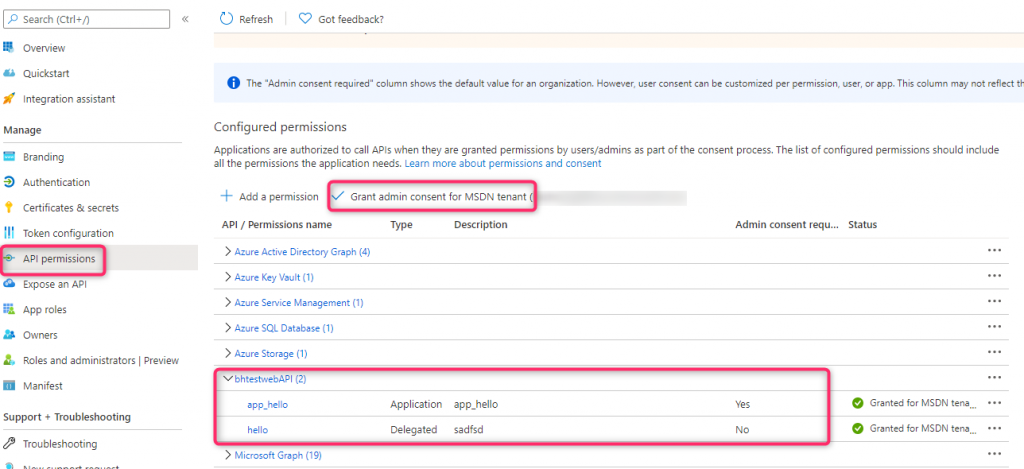
For testing purposes, I have another client app registered and configure the ‘API permissions’ blade with this Web API’s delegated and application permissions. Note: you need to grant admin consent to these permissions before requesting an access token.
Configuring the Spring Boot Web API project
The complete source code for this project is located here. The sample uses maven and Java version 11 as indicated in the pom.xml file. For more info on how this sample code was constructed refer to our Azure AD Spring Boot Web API sample at azure-sdk-for-java/sdk/spring/azure-spring-boot-samples/azure-spring-boot-sample-active-directory-resource-server at main · Azure/azure-sdk-for-java (github.com). Below are the main things you need to configure for the web API project
application.properties file
Put your Application Registration info (Application ID, Tenant ID, and App ID URI) in this file as below:
azure.activedirectory.client-id=<Web API Application ID> azure.activedirectory.app-id-uri=<Web API App ID URI> azure.activedirectory.tenant-id=<tenant ID>
The Controller (Restful) Method(s)
For delegated permission, you need to use ‘SCOPE_<Delegated Permisssion Scope Name>’ in the PreAuthorize’s hasAuthority Annotation, while for application permission, use ‘APPROLE_<Application Permission Scope Name>’ in the PreAuthrorize annotation instead of. I have a few different routes defined in this sample: webAPIA route will only accept Delegated Permission token, webAPIB route will only accept Application Permission token, and webAPIC route will accept either type.
@RestController
public class HomeController {
@GetMapping("/webapiA")
@ResponseBody
@PreAuthorize("hasAuthority('SCOPE_hello')")
public String fileA() {
return "Response from WebApiA.";
}
@GetMapping("/webapiB")
@ResponseBody
@PreAuthorize("hasAuthority('APPROLE_app_hello')")
public String fileB() {
return "Response from WebApiB.";
}
@GetMapping("/webapiC")
@ResponseBody
@PreAuthorize("hasAnyAuthority('APPROLE_app_hello','SCOPE_hello')")
public String fileC() {
return "Response from WebApiC.";
}
}
Build and Run the project
I use the following commands to build and run this Spring project, respectively
mvn clean package -DskipTests
mvn spring-boot:run
Testing the web API
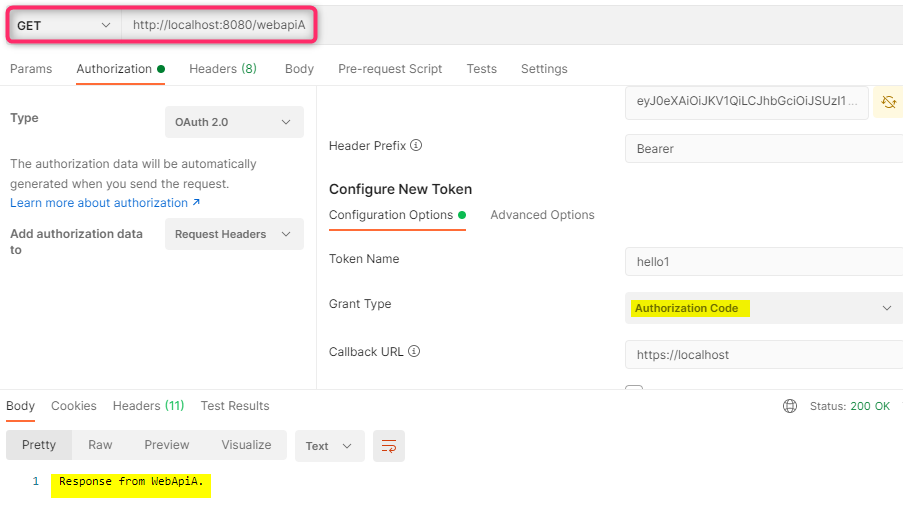
To test the web API, I use PostMan’s built-in feature to get a Delegated permission token using Authorization Code Grant flow and then use the token to call the Web API.
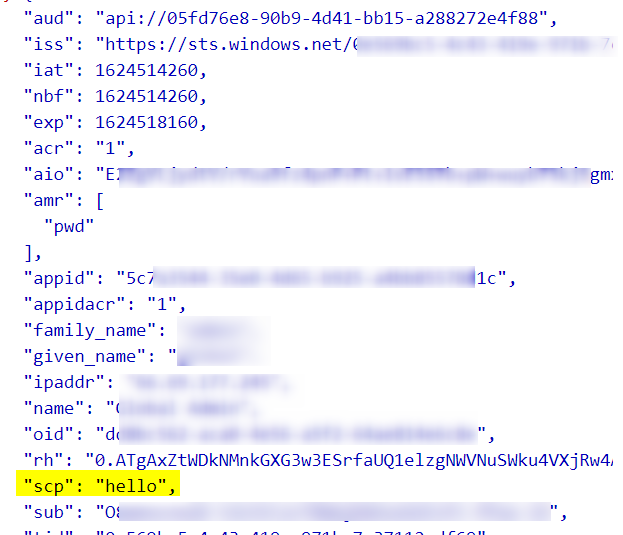
Note: For delegated permission token, the permission shows up in the scp claim (decoded using https://jwt.ms)
Sending the request to webAPIA Route:
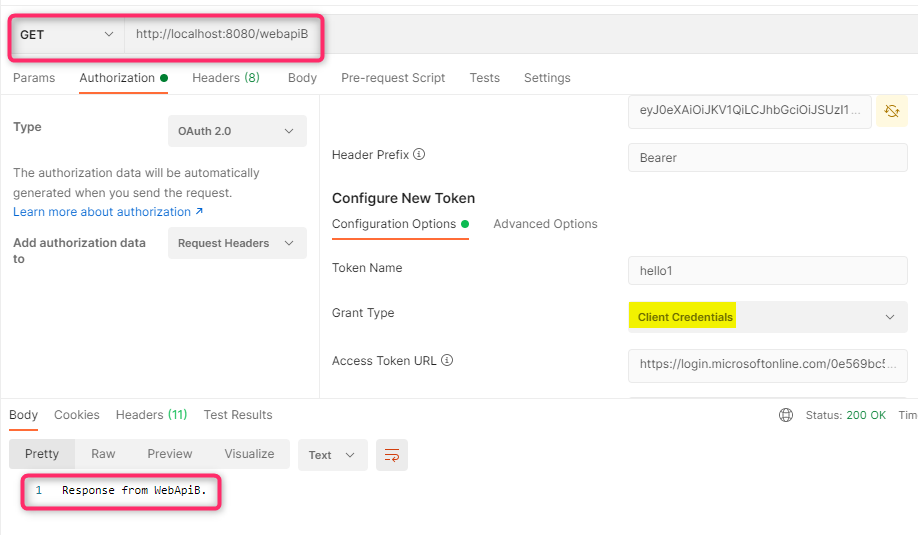
For Application permission testing, I use PostMan’s built-in feature to get an Application permission token using Client Credentials Grant flow and then use the token to call the Web API.
For Application permission token the permission is in the roles claim

Sending the request to webAPIB Route: