In OpenId Connect (OIDC) we have the UserInfo endpoint, that’s specifically for the OIDC protocol and we cannot use with OAuth2 protocol.
To use this endpoint in Azure AD we need a token, and without specifying the “Resource” parameter.
How to obtain a token (V1)
For the sake of this example we’ll use the auth code grant flow to request tokens, using Microsoft Identity Platform V1 endpoint.
In a browser we can request a token like the samples below.
- Request Code – without specifying the “Resource” parameter, like:
https://login.microsoftonline.com/{tenant}/oauth2/authorize?client_id={appid}&scope=openid%20offline_access%20profile&redirect_uri={redirect_uri}&response_type=code
Response:
https://localhost:44555/?code=AQABAAIAAAAP0wLlqdLVToOpA4kwzSnx6BjceMnEMcvAOdHgnHs3FJWDCqJbpVc5kQWtNUD8X-bUSCT1iiYd_vmY-G6nA2RPJK7C1GnSclx3UmUvIQWrANdZfoEZGY_sfTOvZ5Y6S3FVZExIue-vj89JAcJ40nMRBN…
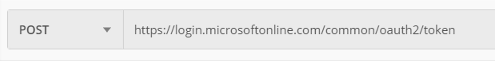
- Request Token – using Code returned request Access Token again, without specifying the “resource” parameter, request to token endpoint should look like:
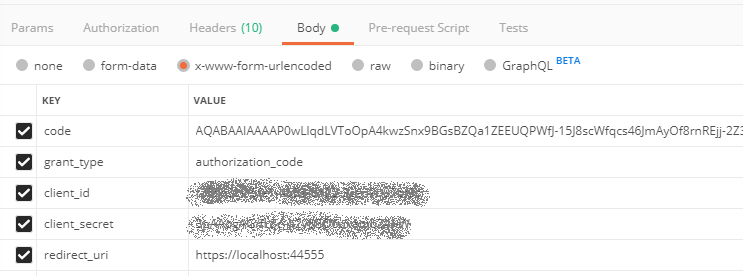
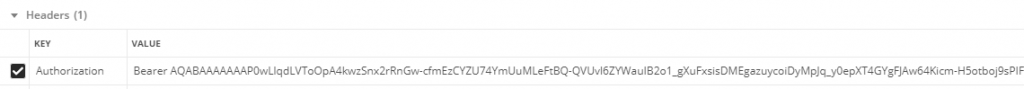
Response has an Access Token, that cannot be decoded:
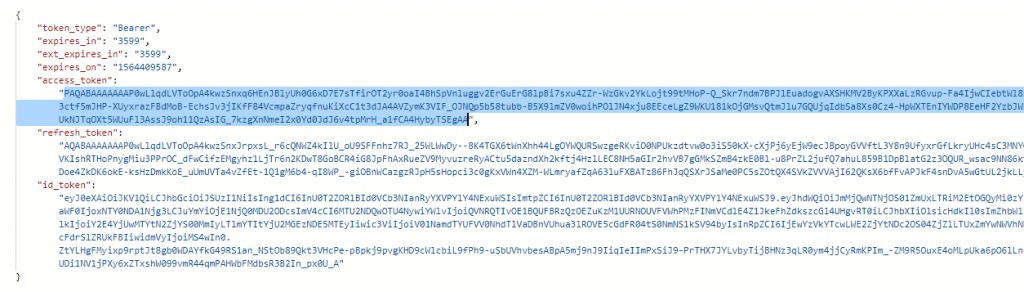
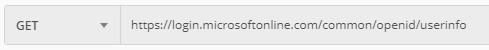
Call the endpoint
Do the request to UserInfo endpoint (https://login.microsoftonline.com/common/openid/userinfo) using the access token, like you can see below:
Response:

Call UserInfo with Microsoft Identity Platform V2 endpoint
Above we described how to call the endpoint using the V1 endpoint, the same can be achieved using the V2 endpoints also.
When using this authentication endpoints we’ll need to get a token with the MS Graph scope and call the UserInfo endpoint – https://graph.microsoft.com/oidc/userinfo.
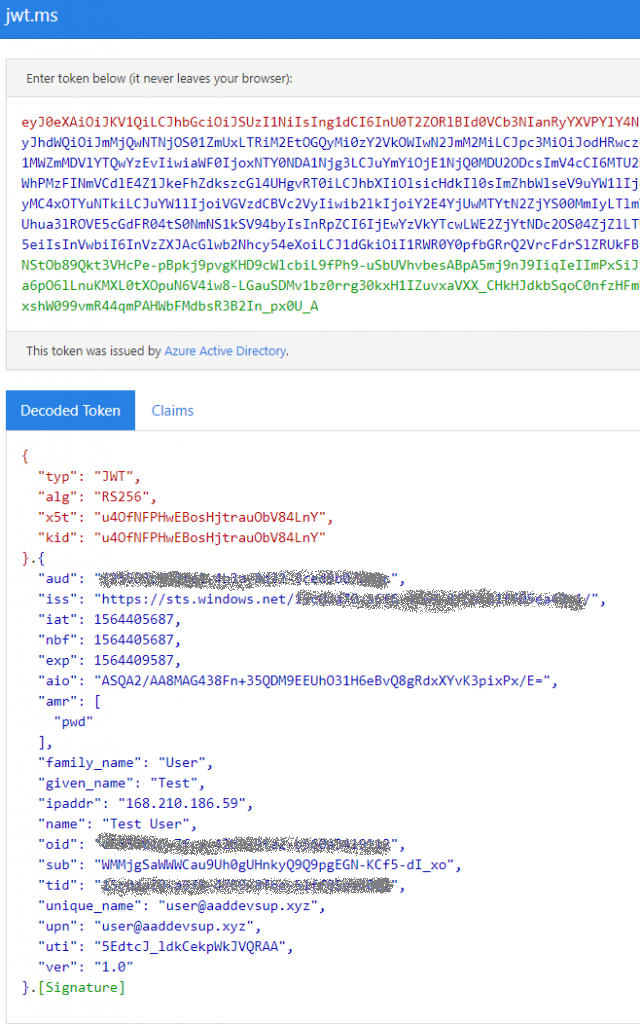
How to get UserInfo details from the JWT Token
If you are requesting a id_token to begin with, you can just decode it and save yourself an additional call in your application.
Below we can see a decoded id_token and information that it has.
Existing endpoints
The information of the UserInfo endpoint that you should use depends on the authentication endpoints version. And the best way to get that info is to call the metadata endpoints.
| Metadata | UserInfo | |
| V1 | https://login.microsoftonline.com/{tenant}/.well-known/openid-configuration | https://login.microsoftonline.com/common/openid/userinfo (Azure AD UserInfo) |
| V2 | https://login.microsoftonline.com/{tenant}/v2.0/.well-known/openid-configuration | https://graph.microsoft.com/oidc/userinfo (MS Graph UserInfo) |
Hi, we’ve been using OIDC tokens with our application behind AWS ALB, and its been working fine so far until recently it stopped working as UserInfo endpoint not returning everything AWS ALB is expecting as per OIDC protocol, any idea? MSFT has been advising to use /me endpoint but it doesn’t return sub.
Hi Faraz, what was the expected information?
We normally do advise to use /me to obtain user information.
Hi Faraz
did you get it to work? What is exact the userinfo endpoint of the B2C AD?
Hi Lars,
Azure AD B2C does not support userinfo endpoint at this time.
Hi Bac
Thank you for your answer, do you know if there are any plans to support it in the future?
Yes. This will be available in the future. I don’t have an ETA at this point
[…] Retrieving user information from Azure AD’s UserInfo Endpoints […]